As more and more of our lives are online, the chance of encountering a cyberattack increases. One of the most popular versions of cyberattacks today is through ransomware. But what exactly is ransomware, how can we protect ourselves and our data from them, and what do we do if we believe we’ve been infected? Let’s dig into that today!
What is Ransomware?
So, what is ransomware? Ransomware is a type of malicious software (malware) designed to deny access to a computer system and/or the data on said system until the ransom is paid. Think of it as your data being kidnapped, and the kidnappers will only give it back to you if you pony up the money.
There are three main types of ransomware: Scareware, Screen Lockers, and Malicious Encryption Malware. Each has a different level of severity, and only one is mostly unable to be fixed.
Scareware
Scareware is the most commonly seen form of ransomware, putting a pop-up on your device that says that some infection or malware has been found on the device, and claiming the only way to remove it is by paying a specific company a fee.
With this type of ransomware, your files are usually safe and if you continue to use the device, the worst you’ll probably experience is the need to close the popup as it comes back into view. We generally see these coming from random faux-security software and tech support scams.
Screen Lockers
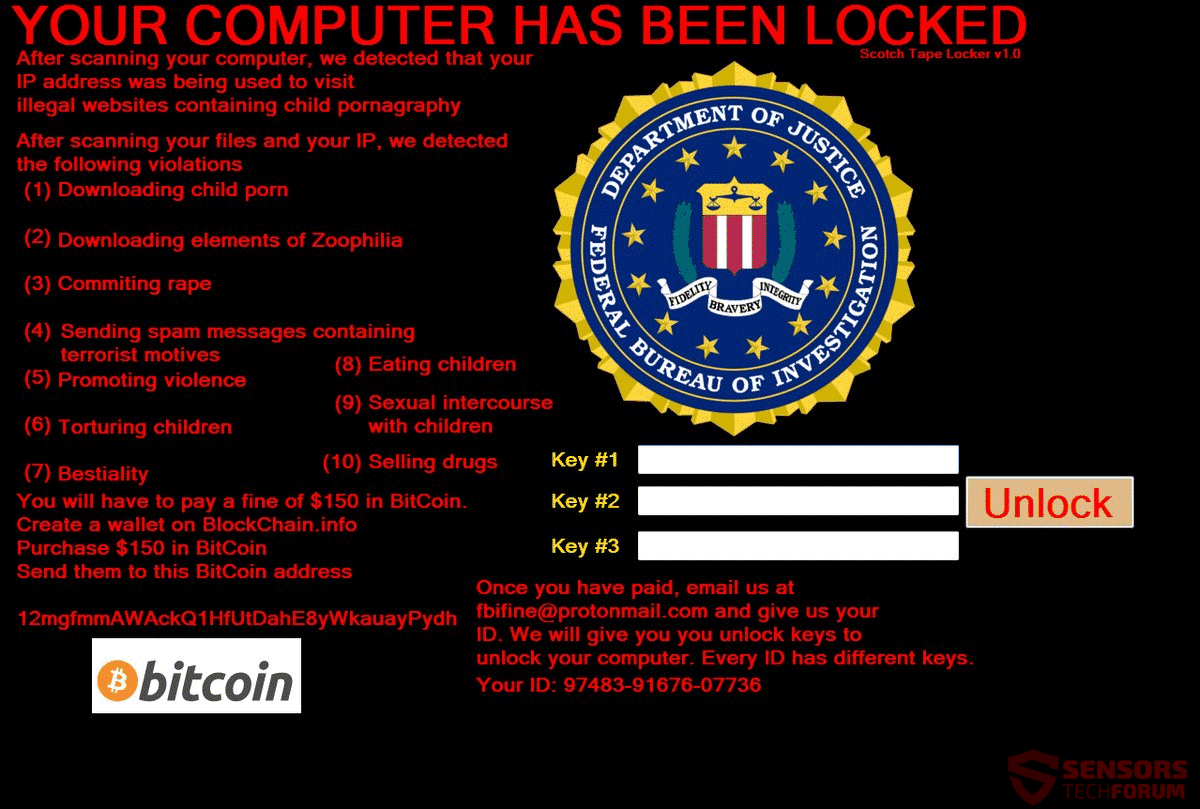
Screen lockers are the next form of ransomware we’re going to cover, and they’re slightly harder to work around. These will attempt to lock you out of your device entirely, generally with an unclosable full-screen window. This window can seem official, with many even having logos from the FBI or the US Justice Department.
Generally, these official logos are paired with some text about how they’ve found you doing something suspicious or illegal online, and you must pay a fine to continue using your device. Generally, a quick trip to your local computer repair specialists can circumvent this problem and leave your device running as good as new.
Malicious Encryption Malware

The final, and most detrimental form of the ransomware covered today, is malicious encryption malware. This type of ransomware encrypts all of your data and will only give you the key to unencrypt it if you pay a fee. Unfortunately, in most cases, if you don’t have a backup of your data, it will be unrecoverable.
What do I do if I’m infected?
With scareware and screen lockers, you can bring them to your local I.T. department (like us), and it’s possible that they can get your device back up and running again. However, if your files have been encrypted, it’s more than likely that you’ll need a complete system wipe and reinstall to remedy the problem. We’d still recommend bringing it into your local I.T. department, as they may have tools and software available to them to further help in this process.
How do I protect myself from ransomware?
The first thing you should do if you want to protect yourself is to get a good cybersecurity program that can detect and prevent cyberattacks in real time. We recommend the premium version of Malwarebytes ($40 per year) to work with your current antivirus to help prevent ransomware.
The next, and arguably the most important step in all cybersecurity, is to stay informed. Be aware of common and current cyberattacks, and know what to look for in order to avoid them. And definitely don’t click on links from sites that you are not familiar with—it only takes one downloaded file to ruin your day.
Right now there are two current ransomware going around called SamSam and Emotet.
While most ransomware families are spread indiscriminately, usually via spam emails or exploit kits, SamSam is used in a targeted fashion. The SamSam group’s modus operandi is to gain access to an organization’s network, spend time performing reconnaissance by mapping out the network, before encrypting as many computers as possible and presenting the organization with a single ransom demand. The attackers have been known to offer to decrypt all computers for a set ransom and/or offer to decrypt individual machines for a lower fee. In many cases, ransom demands can run to tens of thousands of dollars to decrypt all affected computers in an organization. If successful, these attacks can have a devastating impact on victim organizations, seriously disrupting their operations, destroying business critical information, and leading to massive clean-up costs.
From Symantec’s blog post: “SamSam: Targeted Ransomware Attacks”
Emotet is an advanced, modular banking Trojan that primarily functions as a downloader or dropper of other banking Trojans. Additionally, Emotet is a polymorphic banking Trojan that can evade typical signature-based detection. It has several methods for maintaining persistence, including auto-start registry keys and services. It uses modular Dynamic Link Libraries (DLLs) to continuously evolve and update its capabilities. Furthermore, Emotet is Virtual Machine-aware and can generate false indicators if run in a virtual environment.
From the National Cybersecurity and Communications Integration Center (NCCIC).
These are generally targeting hospitals, financial institutions, and governmental infrastructure, but any chance to get information is one where a cybercriminal might be.
The last suggestion (read, you should absolutely do this) is to back up your data to a secure place—preferably one that isn’t directly on the same network as your devices. This way, if something happens to your device, you have a restore point to bring it back to, and you will lose less data and time.
That is just a little bit about Ransomware. I hope this gave you a little bit of information to help protect you while we are living more of our lives in terrifying badlands that the web has become. For more on internet security & scams please check out our other posts: TROJANS & MALWARE & RANSOMWARE, OH MY! – The Necessity of an Antivirus, SEXTORTION: The Latest Internet Plague, Convincing Spam Emails Contain Macro Malware, Your Passwords are the Weakest Link: Here’s How to Improve Them, and Night Of The Living Pop-Up.
